Don't let website security issues put your business at risk.
DreamShield automatically scans your website, detects and blocks malware, and alerts you when something is wrong.

DreamShield detects and blocks thousands of threats every day
All DreamShield protected websites include
Daily Malware Scans
Your website is automatically scanned for malicious software and harmful threats.
Email & Panel Alerts
When we spot something harmful to your website, we notify you right away.
Security Scan Reports
Take action with an emailed summary of detected security issues and recommended next steps.
Software Updated Notices
Stay one step ahead of attackers with proactive software update notifications for over a dozen popular CMS applications, including WordPress, Joomla, Drupal, and more.
File Access Protection
DreamShield detects insecure file permissions and blocks public access to vulnerable files.
Google Safe Browsing
Receive alerts if your website appears on Google's Safe Browsing threat list.
SSL Scans
Detect and resolve problems with your website′s HTTPS certificate.
Suspicious Login Detection
DreamShield notifies you when it detects unusual login activity.
Block Unauthorized Software
DreamShield automatically terminates remote processes running from compromised user accounts.
Rapid detection for rapid recovery
Stay informed about your website's security with automatic daily scanning and instant notifications when a problem is found.
Access detailed scan reports and recommended next steps, and rest assured that DreamHost's support team is just a click away.
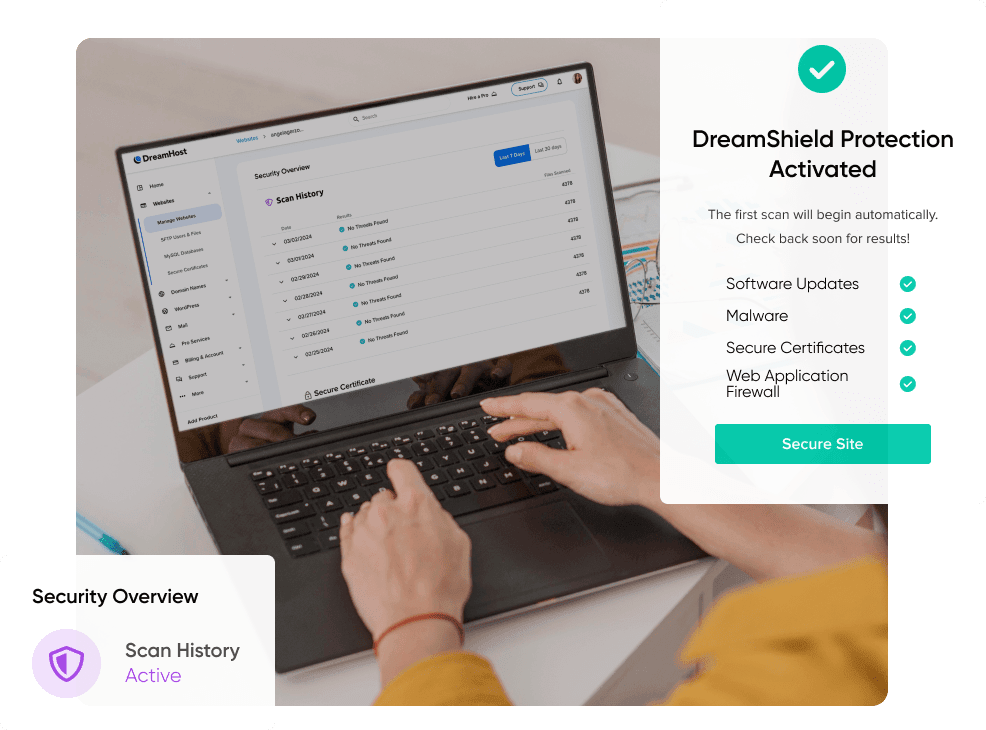
Safeguard your online presence
Harness the power of DreamShield’s comprehensive website protection.

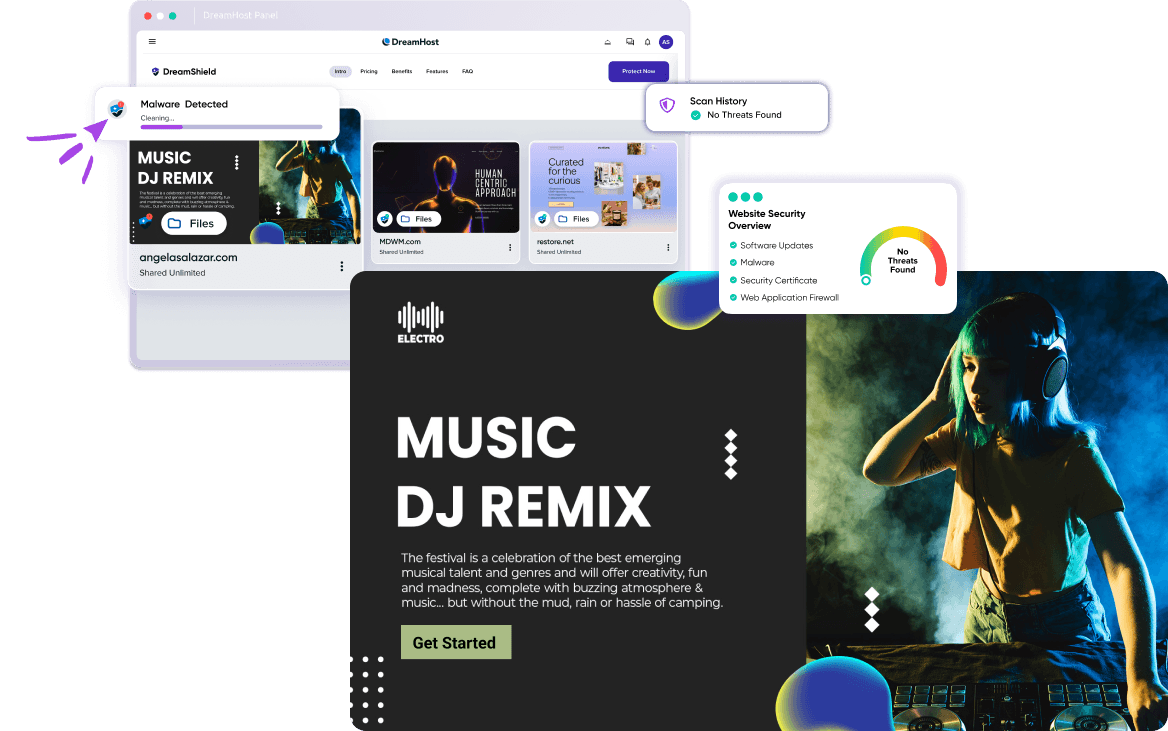
Your Security, At a Glance
The Website Security Overview offers a clear and concise view of your site’s security status, featuring indicators when DreamShield detects outdated software, malware, SSL/TLS errors, and more.
Access and Analyze
Dive deep into your security data with access to the last 30 days of DreamShield scan activity, enabling you to track and analyze trends and threats.
See the Big Picture
Managing multiple websites? No problem. DreamShield integrates seamlessly into the Manage Websites overview, displaying the security health status for all your sites in one convenient location.
For All Skill Levels
Whether you’re a web security expert or new to website management, DreamShield’s user-friendly design makes navigating complex security issues straightforward.
Your site should be protected
Add DreamShield to your new website during signup, or log in to add DreamShield to an existing domain.
Save 16% with a yearly plan!
Just $3.00/mo. per website